8/12/2008
Toll Road Transponder Security HackedSecurity expert proves a toll road transponder can be used to track any vehicle using the device.
A noted computer security expert warns that toll road transponders used by more than a million California motorists could be vulnerable to attack by digital thieves. Nate Lawson, founder of the computer security firm Root Labs, helped design the BD+ copy protection system used on the latest generation Blu-ray discs. When Lawson set out to investigate what privacy protections the FasTrak transponders offered, he was surprised to find there were none.
"The system is very simple to save battery power," Lawson explained in an interview with TheNewspaper.
Each radio frequency id (RFID) transponder sends a unique identification code to scanners positioned at toll booths. A tolling authority computer matches this ID code with credit card and other payment information to collect the toll. It took Lawson just five days take apart and document the internal software functions of the FasTrak transponder that he purchased for $26 at a local supermarket. With this information, he found the ability to read the ID code was not limited to toll booth scanners. An electronics hobbyist could put together an inexpensive RFID scanner to read the ID code of any vehicle remotely, essentially turning the transponder into a homing beacon with a maximum range of about 100 yards.
"You can use it for tracking," Lawson said. "Once you've seen the car, you can pick it out in a crowd."
That is exactly what California's 511 system does. Scanners placed throughout the highway network track the movement of motorists with toll transponders as a means of monitoring traffic flow. According to the California Department of Transportation, the system tracks individual ID codes, storing a movement history for each particular car in a database for 24 hours. Lawson suggested that anyone with access to the 511 database would have the ability to track in real time the movement of any vehicle of interest after having scanned its ID code just one time.
Lawson also documented the method used to reprogram his transponder with another ID code. This raises the possibility that unscrupulous individuals could "clone" the transponder belonging to someone else's account, meaning an innocent driver would be charged for every trip made with the cloned device. Lawson suggested that in a tech-savvy area like the Silicon Valley, it was entirely possible that such cloning may already be taking place. By never using the same ID code twice, a clever ID thief would elude easy detection. Few motorists would go to the hassle of challenging a single stray charge on their FasTrak bill.
Transponder cloning also opens the possibility that the technology could be used to create an alibi for a crime, Lawson warns. Because law enforcement agencies use tracking information from toll transponders to establish the movements of suspects, a clever criminal could clone his own transponder ID code onto someone else's vehicle. That individual would then unknowingly create a driving history that would be attributed to the criminal's vehicle. Lawson found these problems serious, but not insurmountable.
"There are ways to solve it, but it requires more care and discipline," Lawson said.
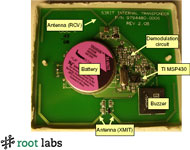
So far, however, the tolling industry has shown little interest in resolving these issues. Instead, before Lawson's findings were presented at the Black Hat technical security conference last week, tolling industry insiders attempted to discredit Lawson by claiming that new ID codes could not be written to the transponder. One report published in an industry newsletter called the claim "baloney" and insisted the FasTrak is a read-only device. Lawson's response was simple. The transponder contains a MSP430F1111A microcontroller chip. Documentation from the chip's manufacturer, Texas Instruments, establishes that it uses flash memory -- meaning it can be reprogrammed. Even the documentation from Sirit, the company that puts together the FasTrak transponder itself, confirms that, "each transponder is RF-programmable allowing a unique ID and vehicle classification to be programmed to customer's specifications."
Lawson has not investigated whether the same vulnerabilities apply to systems used in other areas of the country such as EZ-Pass or SunPass. Lawson says his goal is not to oppose tolling, but to raise awareness about a serious security issue that affects consumers.
"I actually don't have a problem with tolls for road use," Lawson said. "I'm not an advocate for 'everything should be free.' I just think the implementation is bad."
To help address the problem, Lawson intends to create a privacy kit that would allow motorists to switch off their transponder when not in use. The plans for this kit would be made freely available on the Internet.


